Read at least two 2 academically reviewed articles on cyber security and risk management and complete the following activities.
Cyber security and risk management articles.
Professor may check originality of all posts.
Please use your own words.
Please use your own words.
Based on your article review and the assigned reading discuss the relationship between cybersecurity and risk management.
Read at least two 2 academically reviewed articles on cyber security and risk management and complete the following activities.
Professor may check originality of all posts.
Furthermore cyber attacks were the number one concern of executives in european and other developed countries according to a recent.
Summarize the two 2 articles in 300 words or more.
Base on your article review and the assigned reading discuss the relationship between cyber security and risk management.
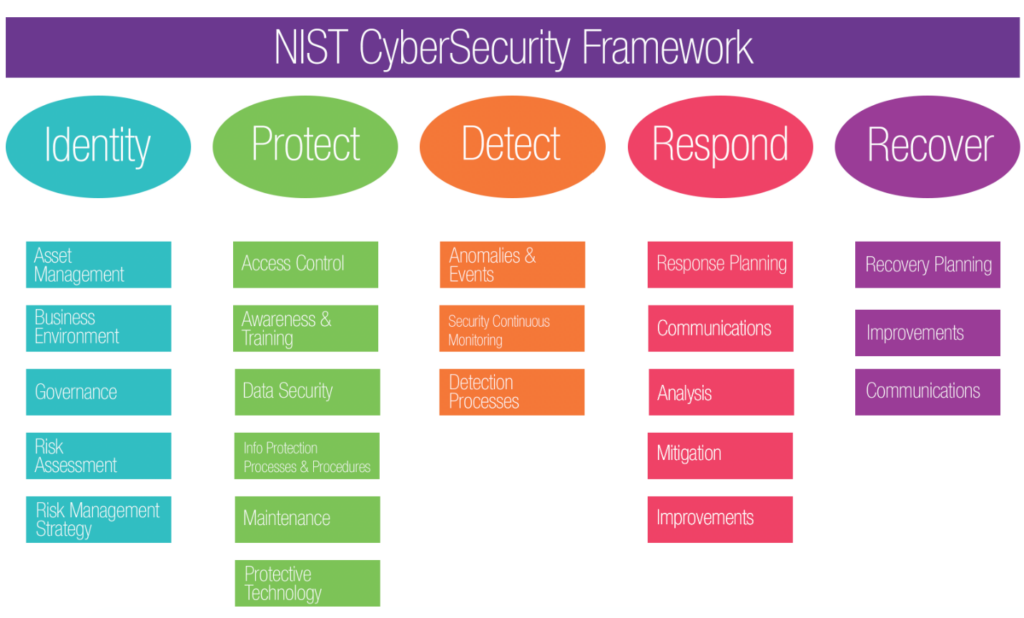
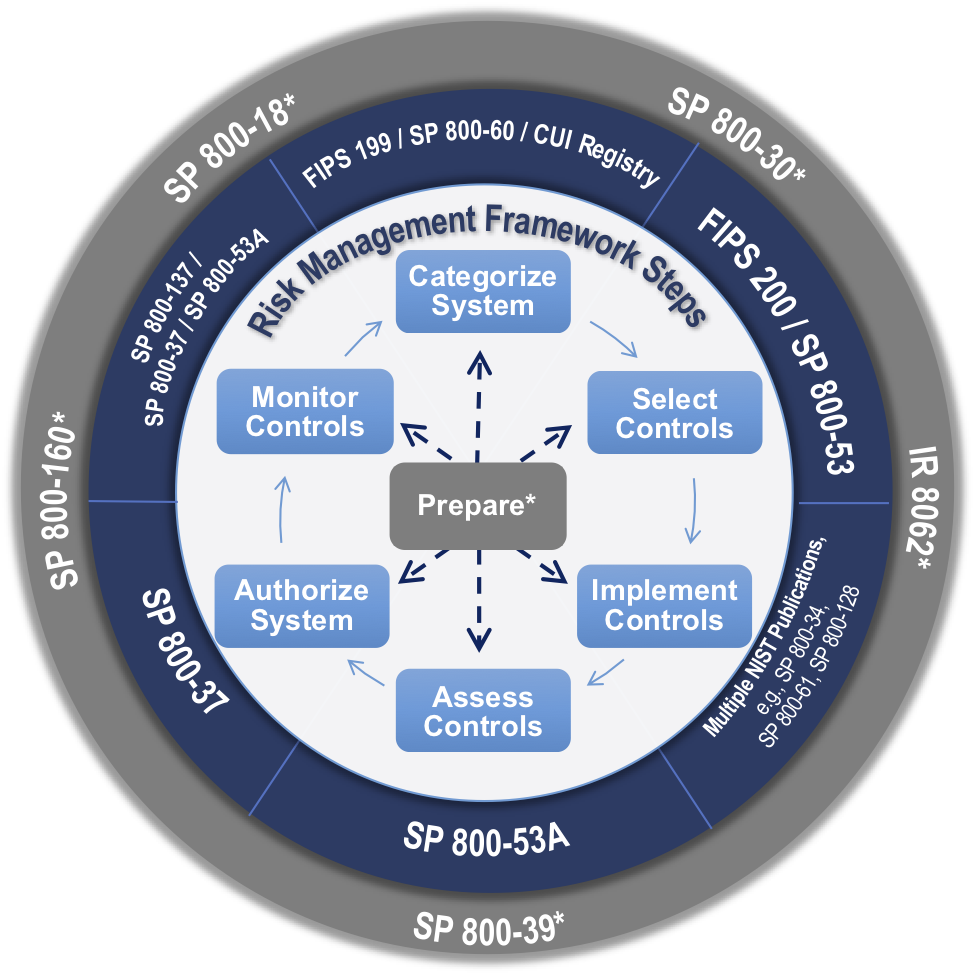
Cybersecurity should be integrated into the overall risk management process of every government organization e g jurisdiction department or agency.
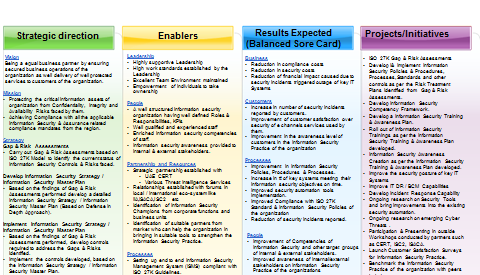
Dashboards are used in thousands of businesses every day.
Cybersecurity reports by cisco show that thirty one percent of organizations have at some point have encountered cyber attacks on their operations technology.
Top 10 cybersecurity risk for 2019 the cyber threat environment is becoming more dangerous every day.
As an it manager discuss how you will use the concepts discussed in the four articles in the management of it risks within your company.
Summarize the two 2 articles in 300 words or more.
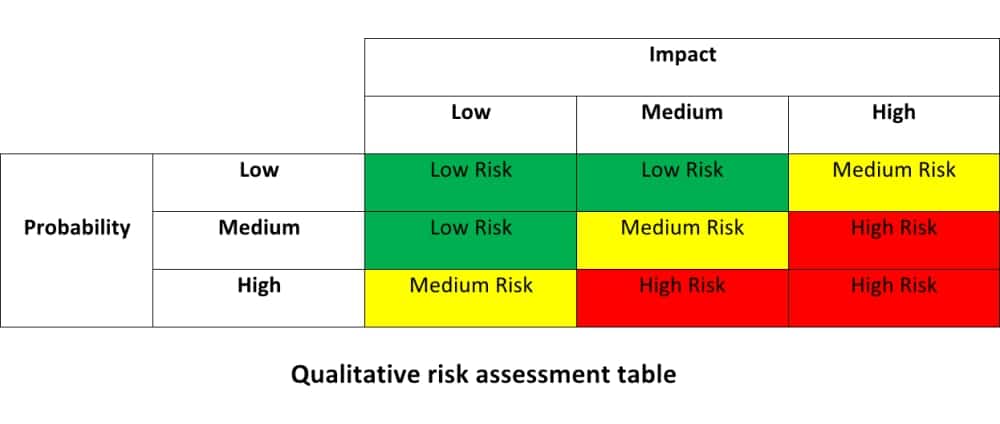
Generically the risk management process can be applied in the security risk management context.
Improve your ability to manage cyber risk.
Base on your article review and the assigned reading discuss the relationship between cyber security and risk management.
As an it manager discuss how you will use the concepts discussed in the four articles in the management of it risks within your company.
Sessions will include interactive incident management session best practices to integrate risk and it and understanding cyber risk and human behaviour.
When it comes to cybersecurity organizations face a future in which it s best to prepare for worst case scenarios.
Summarize the two 2 articles in 300 words or more.
Security risk management security risk management provides a means of better understanding the nature of security threats and their interaction at an individual organizational or community level standards australia 2006 p.
21 sep 2020 24 sep 2020 online virtual.
Dashboards are used in thousands of businesses every day.
Read at least two 2 academically reviewed articles on cyber security and risk management and complete the following activities.
Wikipedia articles will not be accepted.
As an it manager discuss how you will use the concepts discussed.